BLOG
Why Cloud Security Matters for Your Business
You moved to the cloud for speed, scalability and savings. You stayed because it gave you flexibility, faster deployments and easy access across teams. But while the benefits are real, so are the risks. One wrong click or downloading one corrupted file can open a crack—and someone out there is always looking to slip through it.
Let’s be blunt. Cybercriminals don’t care how small or big you are. They only care about one thing: access. And if your cloud environment gives them an easy way in, they’ll take it without hesitation.
Protecting Your Business in the Cloud: What’s Your Role?
The cloud gives you the flexibility to run your business from anywhere, the efficiency to enhance your team’s performance and a strategic edge to stay ahead of competitors without a huge cost.
But here’s the thing—it’s not all sunshine and rainbows. Business on the cloud carries risks that cannot be ignored.
Business owners often have this misconception that once their data is in the cloud, it’s fully protected by the cloud service provider. But that’s not quite how it works. Instead, it’s more of a team effort, and you have a crucial role to play.
3 Reasons to Partner with an Excellent IT Service Provider
Running a business is a balancing act. You’re constantly managing growth, operations and security while trying to stay competitive. But as technology evolves, so do the challenges. Cyberthreats are more sophisticated, compliance requirements keep changing and downtime is more expensive than ever. Without the right IT expertise, these challenges can slow you down.
That’s why you need to turn to IT service providers. They don’t just handle tech issues when something breaks. They help you prevent problems, streamline operations and ensure your IT investments work for your business. Let’s take a closer look at why partnering with an IT service provider must be a top priority.
The Hidden Costs of Reactive IT: Why a Proactive Approach Is Worth the Investment
Issue resolution: It's like an endless loop where your team is always in fire-fighting mode. You’re constantly busy responding to emergencies and unplanned outages. You have no time to focus on strategic initiatives, as your resources are being spent attending to roadblocks.
What it costs you: Lost productivity.
Short-term solutions: If there's a crack in your ceiling, it needs repair and your full attention. A quick fix won't make the issue go away. In IT, if you don't address the root cause of a problem, your tech problems pile up, resulting in fragmented and inefficient technology management.
What it costs you: Increased inefficiencies.
Bonus Blog
Most businesses don’t realize it, but employees, vendors and even software applications often have more access than they need. This might seem harmless until a cybercriminal gets in. The more doors left open, the easier it is for an attacker to move deeper into your systems.
The Principle of Least Privilege (PoLP) is a simple but powerful fix. It limits access based on necessity, restricting users, vendors and applications to only what they need to do their jobs—nothing more, nothing less.
This isn’t just about cybersecurity. It’s about reducing risk, protecting sensitive data and keeping your business running smoothly.
Top 4 Challenges to Achieving Cyber Resilience and How to Overcome Them
No business today is completely safe from cyber threats. Attack vectors are constantly evolving, and despite your efforts, even a simple oversight can leave your business vulnerable to a breach. That's why cyber resilience is so critical, as the very future of your business depends on it.
It's no longer just about preventing cyberattacks but also how you prepare your business to respond to and recover from potential cyber incidents when they do occur.
However, achieving cyber resilience comes with unique challenges, which we'll explore in this blog. But first, let's understand why businesses must implement cyber resilience.
A Deep Dive Into the Six Elements of Cyber Resilience
The reality of a cyberattack isn’t a matter of if but when. The threat landscape has grown increasingly complex, and while traditional cybersecurity focuses on prevention, it’s not enough to combat every potential breach. If a cybercriminal outsmarts your security strategy, you want your business to make it out on the other side.
That’s where cyber resilience comes into play—a strategic approach that equips businesses to anticipate, withstand, recover from, and adapt to cyber incidents. Think of it as your business’s ability to bounce back stronger, ensuring continuity no matter what comes its way.
The question is: Are you ready to make your business resilient? If you are, it’s time to focus on the core elements of cyber resilience to safeguard your business and protect what matters most.
Third-Party Risks: How You Can Protect Your Business
Vet your vendor: Before signing a contract, thoroughly vet your vendor. Don't commit to them without conducting background checks, security assessments, reviews of track records, and evaluation of security policies. Also, ask for certifications and evidence of compliance with industry norms.
Define expectations: You can't take a chance on your business. Draw up a contract that clearly outlines your expectations on security, responsibilities, and liabilities. Ensure you have a clause that makes it mandatory for the vendor to maintain specific security standards at all times and makes them obligated to report any or all security incidents.
How IT Service Providers Can Help Manage Your Third-Party Risks
Risk assessment and due diligence
Knowing where risks exist is the first step to managing them. IT service providers can conduct thorough evaluations of your vendors. They don’t just stop at surface-level checks; they dig deep into compliance records, past security incidents and their existing vulnerabilities.
This isn’t about instilling fear. It’s about giving you clarity. When you understand which vendors pose risks and where your vulnerabilities are, you’re in a much stronger position to decide which partners to trust and how to protect your business.
The Role of Leadership in Cyber Awareness: How Business Leaders Can Set the Tone
You invested in the latest security software and even hired a great IT team. However, one misstep by an unsuspecting employee and a wrong click on a malicious link later, you are staring at a costly breach that threatens to jeopardize the future of your business.
The best way to secure your business isn't just through firewalls or antivirus alone. Your employees also play an equally critical role in protecting your business. When employees lack adequate security training, they can become easy targets and fall prey to phishing scams or malicious malware.
Cybersecurity Starts With Your Team: Uncovering Threats and the Benefits of Training
When you think about cybersecurity, your mind might jump to firewalls, antivirus software, or the latest security tools. But let’s take a step back—what about your team? The reality is that even with the best technology, your business is only as secure as the people who use it daily.
Here’s the thing: cybercriminals are intelligent. They know that targeting employees is often the most straightforward way into your business. And the consequences? They can range from data breaches to financial losses and sleepless nights.
So, let’s break this down. What threats should you be worried about, and how can regular training protect your team and business?
Common Risk Assessment Myths That Every Business Owner Needs to Know
Despite believing they were immune, a small law firm in Maryland fell victim to a ransomware attack. Similarly, an accounting firm in the Midwest lost all access to its client information, financial records and tax files. They assumed that antivirus software was all the security they needed to thwart a cyberattack.
In both incidents, the victims coincidently were small businesses and fell prey to sophisticated cyberattacks because of their flawed risk assessment practices.
Business owners have several misconceptions about IT risk assessments that leave them vulnerable. This blog will uncover common cyber risk assessment myths and discuss the reality. We’ll also show you how to build an adequate risk assessment strategy by the end.
Risk Assessments: Your Business’s Pitstop for Growth and Security
Running a business is like being in the driver’s seat of a high-performance car. It’s fast-paced, competitive, and full of passion. But even the best racecars can’t go far without regular pitstops.
Skipping those necessary checks is like failing to assess the security risks in your business. You may initially save time, but at what cost?
Risk assessments are essential for identifying risks and maintaining asset safety and efficiency to keep your business at its peak. Without them, you leave your business vulnerable.
Build a Strategic Tech Plan That Fuels Business Growth and Profit
Every business, regardless of its size, aspires to grow. To make this happen, business owners work tirelessly to build the right strategy to promote growth and drive profit. Unfortunately, many businesses find it challenging to keep up with the demands of a technology-driven space.
We’ve compiled this blog to show you how to build a strategic technology plan that aligns with your critical business goals and delivers maximum return on investments (ROI). We aim to empower you to create an effective tech strategy that optimizes investments and gives a competitive edge.
Tech Planning and Budgeting: A Winning Combination for Your Business
A solid tech plan is non-negotiable for any business that wants to succeed in today’s competitive tech landscape.
When paired with effective budgeting, this plan ensures that your technology investments align with your organizational goals and make the best use of your resources.
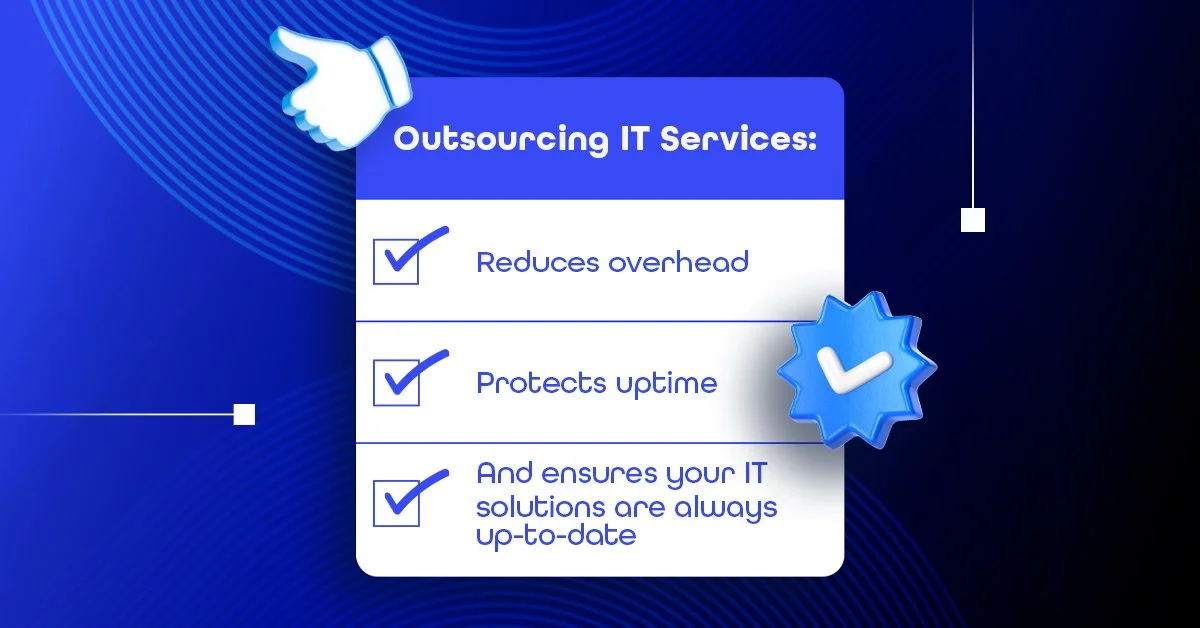
Benefits of outsourcing IT
Today's businesses depend heavily on technology for success and growth. However, navigating complex tech issues and ensuring all your systems stay up-to-date can be overwhelming, especially if you have to manage IT on your own.
That's why you need a strategic ally -- a reliable IT partner -- who supports you through thick and thin. In this blog, we'll show you how an exceptional IT service provider works hard to ensure you achieve your business goals.
Good vs. Great
Technology is critical in driving business success in today’s fast-paced digital landscape. However, managing IT infrastructure and systems can be a significant challenge for many organizations.
This is where an IT service provider comes in. But remember that not all IT service providers are created equal.
While a good IT service provider might ensure that your systems are running efficiently, a great IT service provider can elevate your business to new heights.
AI in Cybersecurity Part 2
AI has become a buzzword that often evokes a mix of awe, doubt and even fear, especially when it comes to cybersecurity. However, the fact is that if used effectively AI can revolutionize the way businesses like yours operate.
That’s why you must cut through the noise and separate fact from fiction if you want to leverage AI effectively. In this blog, we'll debunk some common misconceptions about AI in cybersecurity.
AI in Cybersecurity Part 1
Managing a business on your own is challenging enough without worrying about cyberattacks. However, there is cause for alarm as hackers are using artificial intelligence (AI) to launch sophisticated cyberattacks to steal your data and disrupt business operations.
The good news is there are steps you can take to protect your business. This blog will explain how AI is being used in cybercrime and how you can safeguard your business.
Incident Response Level-Up
Are you prepared to face a cybersecurity breach, a natural disaster or a system failure?
Such disruptive events can strike at any moment, causing chaos and confusion.
But don’t worry. With an effective incident response plan in place, you can handle any incident with confidence.